Incident Overview
- Date: September 3, 2024
- Incident: Exploitation of the Penpie platform, resulting in the theft of 11,113.6 ETH (~$27,348,259).
- Mitigation: Deposits and withdrawals paused; frontend restoration completed.
On September 3, 2024, at 6:23 PM UTC, a sophisticated attacker exploited a security vulnerability within the Penpie platform, seizing control of users’ funds and draining over $27,000,000 worth of assets across the Arbitrum and Ethereum networks. The attacker manipulated a fake Pendle market to maximize rewards.
Root Cause
The root cause was a reentrancy protection vulnerability in the PendleStakingBaseUpg::batchHarvestMarketRewards() function. By re-entering the PendleStakingBaseUpg::depositMarket() function during the reward harvesting process, the malicious SY contract repeatedly added new deposits sourced from flash loan. This allowed the attacker to manipulate the reward token and their amounts sent to the fake Pendle market depositor, which is the attacker itself.
Penpie’s open system for permissionless registration of new Pendle markets triggered this fraudulent activity, the design of permissionless registration itself is fine, but it allowed the attacker to register a fake Pendle market with an attack SY contract and execute the exploit, which uncovered the reentrancy vulnerability.
Loss Analysis
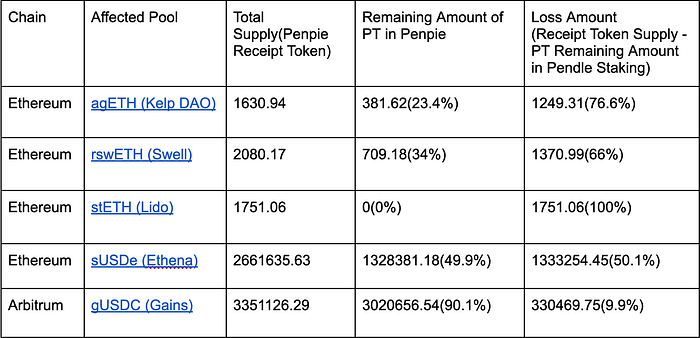
Affected pools on Penpie:
Timeline (UTC)
September 3, 2024
5:44 PM — 5:51 PM UTC
Attacker deploying malicious Pendle Market contracts and deposit on Penpie preparing for attack:
- https://etherscan.io/tx/0xfda0dde38fa4c5b0e13c506782527a039d3a87f93f9208c104ee569a642172d2
- https://etherscan.io/tx/0x7e7f9548f301d3dd863eac94e6190cb742ab6aa9d7730549ff743bf84cbd21d1
- https://etherscan.io/tx/0x7961b0d3382bddff4c777e432902ea0b6940414ec16aa1a1dcebc4ebcbd8f867
- https://etherscan.io/tx/0xca87f257280e19378dc1890a478514195f068857affacde0b92c851b897dff9e
6:23–6:42 PM UTC
- The first attack on Penpie occurred via Ethereum. (TX) (Exploiter address)
- Attacker proceeded to drain more funds via Ethereum (TX)
- Attacker continued draining funds via Ethereum (TX)
6:45 PM UTC
Pendle fully paused their platform on Ethereum
7:00 PM UTC
The Pendle team informed us that Penpie had been exploited by an attacker.
7:10 PM UTC
Hexagate notified us that Penpie had been exploited, and we initiated an investigation in collaboration with them.
7:14 PM UTC
Last drained funds were stolen by the attacker via Arbitrum ($621k gUSDC) TX
7:19 PM UTC
Pendle fully paused their platform on Arbitrum
7:27 PM UTC
Pendle posted on X, informing users that their platform was unaffected. However, they also reported that Penpie had been targeted by an attacker and a security compromise was found.
7:38 PM UTC
The Penpie protocol was paused on all chains
7:53 PM UTC
Penpie Team joined a War Room with Pendle Finance and the Security Alliance (SEAL 911)
7:55 PM UTC
We announced on X that a security compromise was encountered in the Penpie platform.
8:16 PM UTC
Exploiter transferred 11,109.62 ETH into a new wallet (TX)
9:15 PM UTC
After various confirmations, we announced on X that all other protocols within the Magpie ecosystem were unaffected and secure.
10:20 PM UTC
The Penpie team arrived at the Kampong Java Neighbourhood Police Centre (N.P.C.) in Singapore to file a report on the incident.
11:01 PM UTC
Exploiter transferred funds to other addresses, split in batches of 1,000 ETH (TX)
11:06 PM UTC
The Penpie team is working on restoring the platform’s frontend.
September 4, 2024
12:27 AM UTC
AstraSec shared the root cause and loss report to Penpie.
1:21 AM UTC
An onchain message was sent to the hacker encouraging him to resolve the issue without law enforcement. (TX)
2:12 AM UTC
The Penpie team filed an IC3 report on the ic3.gov website.
2:28 AM UTC
We sent a message to the hacker via a public post on X, encouraging him to return funds in an amicable manner with the commitment of solving the issue without pushing for any legal action.
3:29 AM UTC
- Exploiter transferred 11,103.60 ETH to a new address (TX)
- Exploiter transferred 10 ETH to the same new address (TX)
3:38 AM UTC
We have begun collaborating with Hypernative to track the hacker’s activity.
5:00 AM UTC
Held an in-person meeting with Match Systems to assess the situation and explore available options.
5:19–8:03 AM UTC
Initiated communication with Binance Security, Slowmist, and Chainalysis/zeroShadow to demix the Tornado Cash deposits.
Response and Mitigation
- The Pendle Finance contract was paused shortly, effectively safeguarding approximately ~70$ million (excluding vePendle position) that could have been further drained from Penpie.
- The Penpie contract was paused to prevent any additional malicious pool registrations and further potential attacks on Penpie.
- Continuous tracking of the stolen funds and the attacker’s activities.
- The Penpie frontend on the Ethereum and Arbitrum chains was fixed about three hours after the incident.
- Legal Action: Active collaboration with law enforcement agencies is underway to identify and apprehend the attacker.
- Communication: On-chain messages were sent to the hacker multiple times, seeking a whitehat negotiation, but no response has been received so far.
- Transparency: Updates have been provided to the community regarding the status of deposits, withdrawals, and other relevant developments.
Technical Details:
Penpie is the yield boosting layer on top of Pendle Finance, users can deposit Pendle Finance Market Token on Penpie to earn boosted PENDLE incentives.
There are two major factors that together caused the incident:
- PendleStakingUpg.batchHarvestMarketRewards, which lacked reentrancy protection.
- Penpie treated all Pendle Markets as valid pools for registration, while the creation of Pendle Markets, PT, and YT tokens is permissionless.
The major Penpie’s contracts involved in the incident is the PendleStaking https://etherscan.io/address/0x6E799758CEE75DAe3d84e09D40dc416eCf713652 which is the major contract holding all Penpie depositor’s Pendle Market token and vePENDLE position.
The Attack Flow:
1. The attacker first created a malicious Pendle Market with a malicious SY contract. (In this context, the SY contract is the primary contract used to perform a reentrancy attack on Penpie.)
2. The attacker created a pool on Penpie using the malicious Pendle Market.
3. The attacker created a large number of malicious Pendle Markets by minting a significant quantity of fake YT and SY tokens.
4. The attacker deposited a large number of malicious Pendle Markets on Penpie.
5. The four steps above are demonstrated in: https://etherscan.io/tx/0x7e7f9548f301d3dd863eac94e6190cb742ab6aa9d7730549ff743bf84cbd21d1 (One example)
6. The attacker flash-loaned a large amount of wstETH, sUSDe, egETH, and rswETH from Balancer and parked them in the SY contract (the attack contract).
7. PendleStaking.batchHarvestMarketRewards was invoked on the malicious Pendle Market. During the batchHarvestMarketRewards call, the malicious SY contract returned Pendle Market tokens of wstETH, sUSDe, egETH, and rswETH as reward tokens.
8. Next, the claimReward function on the malicious SY contract is invoked, which deposits the Pendle Market tokens of wstETH, sUSDe, egETH, and rswETH from the flash loan into PendleStaking to manipulate the reward amount. (This step involves a reentrancy attack.)
9. PendleStaking then sent the incorrect reward tokens (Pendle Markets) and amounts to the RewardDistributor, attributing those Pendle Markets to the fake Pendle Market depositor.
10. Since the attacker was the only depositor in the fake Pendle Market, was able to claim all the rewards, including wstETH, sUSDe, egETH, and rswETH Pendle Market tokens.
11. The attacker withdrew from the fake Pendle Market and also converted the Pendle Market tokens of wstETH, sUSDe, egETH, and rswETH back into their original asset forms.
12. The above fund drawing steps are done in txn https://app.blocksec.com/explorer/tx/eth/0x56e09abb35ff12271fdb38ff8a23e4d4a7396844426a94c4d3af2e8b7a0a2813 (One fund draining txn example)
Penpie Audit History
1. Upon Penpie’s launch in June 2023, PendleStakingbaseUpg.batchHarvest was not mentioned in Zokyo’s audit report but was noted in WatchPug’s audit report. In WatchPug’s report, the concern was incorrect distribution, as pendlemarket.redeemRewards() was able to claim rewards on behalf of any user. The issue was marked as resolved after we added a manual reward distribution mechanism to PendleStakingbaseUpg.
In Zokyo’s and WatchPug’s reports, there was no mention of reentrancy protection. This was likely because all Pendle Market registrations on Penpie were restricted to the contract owner (the Multisig of the Penpie team) at that time, mitigating concerns about reentrancy attacks from a malicious SY contract.
2. Around one year later, in May 2024, the Penpie team introduced permissionless pool registration, allowing users to register a Pendle Market on Penpie as long as the Pendle Market is registered on Pendle Finance.
The permissionless pool registration feature on Penpie was audited by AstraSec, a different audit firm from the one that audited the initial Penpie smart contract in May 2023. However, since the `PendleStakingBaseUpg` contract did not undergo significant changes after the initial audit, it was not included in the scope of AstraSec’s audit.
- Penpie V1 audit report by Zokyo: https://github.com/magpiexyz/audit/blob/main/Penpie/WatchPug_V1.pdf
- Penpie V1 audit report by WatchPug:
- https://github.com/magpiexyz/audit/blob/main/Penpie/Zokyo_V1.pdf
Incremental audit report by AstraSec:
Next Steps
- Security Audit: Comprehensive review of all protocols and smart contracts to identify vulnerabilities.
- User Communication: Continued transparency with users regarding the ongoing situation and steps being taken to secure their funds.
- Security Collaboration: Working with external security experts and partners to strengthen the platform’s defenses.
- Re-enable Operations Gradually: Once we receive approval from the audit firms on the fix, we will gradually re-enable deposits and withdrawals. We will begin with unaffected pools before fully restoring all deposit and withdrawal functions.
- Compensation: We will begin developing a compensation plan by opening a thread in the governance forum to gather suggestions and feedback from the community. A governance vote will then be created on Snapshot to finalize the compensation plan.
We would like to express our deepest gratitude to our users for their patience, understanding, and continued trust during this challenging period. The security of your assets and the integrity of our platform are our top priorities, and we are fully committed to recovering the stolen funds. Our team is working around the clock to address every aspect of the situation, from tracking the attacker’s activities to collaborating with law enforcement and security experts.
We deeply acknowledge the significant impact this attack has had on users from other protocols who had assets deposited on Penpie, including agETH holders from Kelp DAO, rswETH holders from Swell, stETH holders from Lido, sUSDe holders from Ethena, and gUSDC holders from Gains. Please know that your losses are of utmost importance to us. Your assets and trust are our highest priorities, and we are committed to ensuring a fair resolution for everyone affected.
We recognize the critical importance of this matter and are leaving no stone unturned in our efforts to strengthen our platform’s defenses. As we move forward, we will continue to provide transparent updates and ensure that all necessary steps are taken to safeguard your interests. We are also pursuing peaceful resolutions by attempting to contact the hacker directly, while continuing our investigation with security experts and legal enforcement. Your support is invaluable to us, and we are dedicated to restoring your confidence as we make progress in resolving this issue.
We appreciate the support from Pendle, SEAL 911, Hexagate, SlowMist, Binance Security, Hypernative, Match Systems, AstraSec, Peckshield, Chainalysis, zeroShadow and the Singapore Police during this time. Their assistance is invaluable as we work to address and resolve the situation.
Thank you for being an essential part of the Penpie community. We look forward to sharing positive developments with you soon.
About Penpie: Penpie is a Next-Generation DeFi SubDAO created by Magpie XYZ to provide Pendle Finance users with yield and veTokenomics boosting services. Integrated with Pendle Finance, Penpie focuses on locking PENDLE tokens to obtain governance rights and enhanced yield benefits within Pendle Finance. Penpie revolutionizes the way users can maximize their returns on investments and monetize their governance power.
Website / Twitter / Discord / Telegram / Docs / Link3 / Medium / WatchPug Audit / Zokyo Audit / AstraSec

